Understanding Computer Network Protocols: How Many Are There?
Computer network protocols are the backbone of digital communication, enabling devices to exchange information seamlessly. These protocols are essential for facilitating communication between different devices, ensuring data is transmitted accurately and efficiently. Think of them as the rulebook that governs how data travels across the internet.
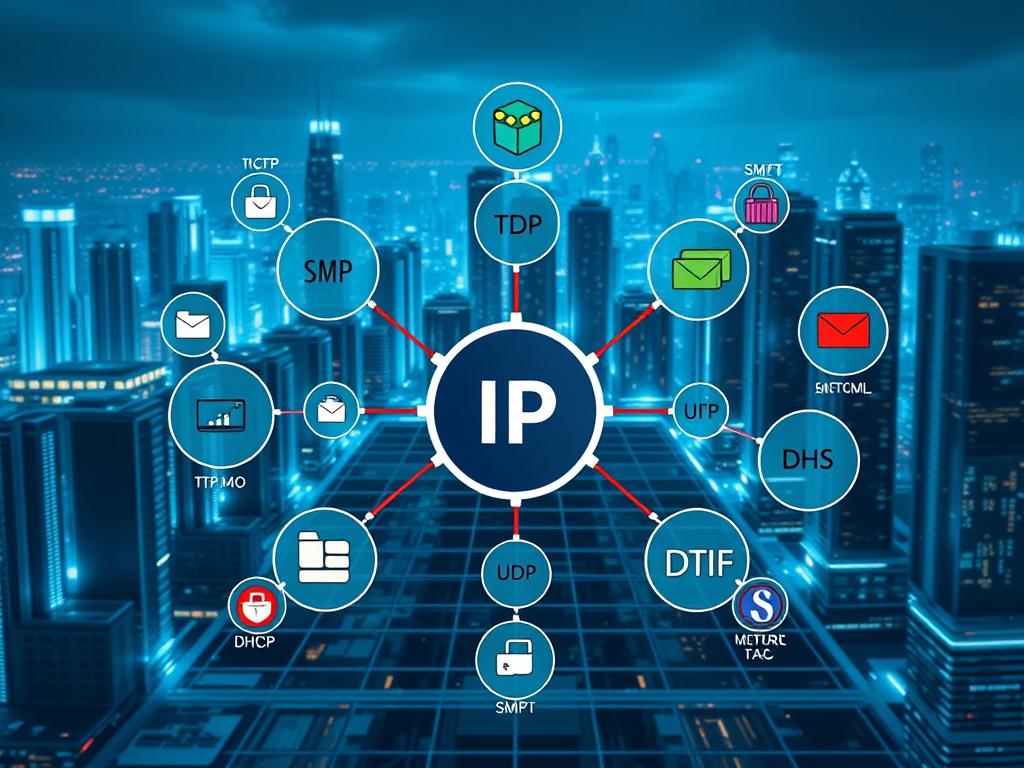
Protocols like TCP/IP and Internet Protocol (IP) are fundamental to modern networking. They dictate how data packets are routed, addressed, and delivered. Without these standardized rules, the internet as we know it would not function. This article delves into the diverse world of network protocols, exploring their types, functions, and evolution.
From communication protocols such as HTTP and FTP to security protocols like HTTPS, each plays a vital role in maintaining network integrity. Understanding these protocols is crucial for anyone involved in networking, whether you’re setting up a home network or managing a large enterprise system.
In this comprehensive guide, we’ll uncover the various protocols that underpin our connected world. By the end of this article, you’ll have a clear understanding of how many protocols exist, their roles, and their importance in maintaining seamless communication across networks.
Introduction to Computer Network Protocols
Network protocols are the essential guidelines that dictate how data is transmitted across devices. They serve as the foundation for efficient and accurate communication in the digital world. Think of protocols as the rulebook that ensures every device understands how to send and receive information.
What Are Network Protocols?
Protocols are predefined sets of rules that govern data transmission. They are crucial for enabling devices to communicate seamlessly, whether it’s a home network or a large enterprise system. These rules ensure that data is packaged, addressed, and delivered correctly. Without protocols, the internet as we know it would cease to function effectively.
How Protocols Enable Device Communication
Protocols facilitate communication by standardising the format of data transmission. They ensure that devices, regardless of their operating system or hardware, can understand and process the information. For instance, communication protocols like HTTP enable browsers to request and receive web pages, while file transfer protocols like FTP allow for secure and efficient file sharing. These protocols maintain consistency, ensuring that data is exchanged accurately and efficiently across diverse systems and hardware.
By understanding network protocols, one can appreciate the intricate mechanisms that power our connected world. Protocols are not just technical jargon; they are the unsung heroes of digital communication, ensuring that every piece of data reaches its destination as intended.
how many protocols in computer network: An Overview
The world of computer network protocols is vast and constantly evolving, making it challenging to pin down an exact number. New transfer protocols emerge regularly, driven by technological advancements. This continuous innovation means the landscape of network communication is always expanding.
Common examples include protocol used like TCP/IP and HTTP. These are essential for enabling devices to communicate and exchange data. Ensuring proper access and a stable connection are critical for seamless communication. Understanding these protocols is key to grasping how modern networks function.
While it’s difficult to count every protocol used, knowing the major ones is crucial. From transfer protocols like FTP to those ensuring secure access, each plays a vital role. A stable connection relies on these protocols, making them indispensable in our connected world.
For a deeper dive into network fundamentals, visit our guide: Understanding Networks in Computer Science.
Communication Protocols: Connecting Devices
Communication protocols are vital for enabling devices to connect and exchange information seamlessly. These protocols ensure that data transmission is orderly and reliable, forming the foundation of modern digital communication.
The Role of TCP/IP and HTTP
TCP/IP, or Transmission Control Protocol/Internet Protocol, is the cornerstone of internet communication. It provides a reliable framework for data transmission, ensuring that information reaches its intended destination intact. TCP/IP is essential for routing data packets across different networks, making it the backbone of the internet. HTTP, or Hypertext Transfer Protocol, plays a crucial role in web communication. It facilitates the sharing of web pages, enabling browsers to request and receive content from servers seamlessly.
Understanding UDP in Real-Time Applications
While TCP/IP offers reliability, UDP, or User Datagram Protocol, prioritizes speed. UDP is ideal for real-time applications like video streaming and online gaming, where fast data transfer is critical. Although UDP does not guarantee delivery, its efficiency makes it perfect for time-sensitive communications.
Comparing these protocols reveals a trade-off between reliability and speed. TCP/IP ensures stable, orderly data transfer, while UDP sacrifices reliability for the sake of efficiency. This distinction makes each protocol suitable for different applications, ensuring optimal performance in their respective domains.
File Transfer Protocol: Secure and Efficient File Sharing
File transfer protocol (FTP) has long been a cornerstone of digital communication, enabling seamless file sharing across networks. This section delves into the evolution of FTP, exploring its traditional form and the more secure alternatives that have emerged to address its limitations.
FTP, SFTP, and FTPS Explained
Traditional FTP is one of the earliest methods for transferring files over the internet. Operating in the application layer of the OSI model, FTP allows users to send and receive files in various formats, including ASCII, EBCDIC, and image files. However, its lack of encryption makes it vulnerable to security threats, prompting the development of more secure alternatives.
Enter FTPS and SFTP, designed to enhance security. FTPS adds a Transport Layer Security (TLS) layer, encrypting data during transfer, while SFTP operates over a secure shell, providing end-to-end encryption. These protocols ensure that sensitive information remains protected from interception and unauthorized access.
Understanding the differences between these protocols is crucial. FTP is ideal for simple, non-sensitive transfers due to its ease of use and support for large file transfers. However, for sensitive data, such as financial records or confidential documents, FTPS or SFTP is recommended. These secure protocols are widely adopted in industries like banking and corporate environments, where data security is paramount.
In summary, while traditional FTP remains a reliable method for straightforward file transfers, the advent of FTPS and SFTP has revolutionized secure file sharing. By choosing the right protocol based on security needs, individuals and organizations can ensure their data remains safe and efficiently transferred.
Internet Protocols: The Backbone of Data Exchange
Internet protocols are the cornerstone of modern data exchange, enabling seamless communication across the globe. These protocols are essential for directing information between devices, ensuring that every piece of data reaches its intended destination efficiently and accurately. Without these standardized rules, the internet would be a chaotic, disjointed system.
How I Addresses and Routing Work
IP addresses are unique identifiers assigned to each device connected to a network, allowing precise routing of data packets. These addresses ensure that information is delivered to the correct destination, much like how a postal address ensures your mail reaches the right house.
Data is transmitted in small, manageable packets, each carrying specific destination information. This process ensures efficient transmission and allows multiple devices to share the same communication channel without data loss or corruption.
Servers play a crucial role in managing and routing these packets. Using stored routing information, servers efficiently direct each packet to its destination. This process is vital for maintaining the seamless operation of the internet, ensuring that every request and response reaches its intended target without delay.
For a deeper understanding of how internet protocols function, visit the Internet Protocol page on Wikipedia.
Network Management Protocols: Monitoring and Control
Effective network management is crucial for maintaining seamless digital communication. Protocols designed for this purpose ensure that networks operate smoothly, allowing administrators to monitor performance and diagnose issues efficiently.
DHCP and SNMP in Action
Dynamic Host Configuration Protocol (DHCP) automates the assignment of IP addresses, significantly reducing manual intervention. This protocol ensures that devices on a network receive the necessary configurations to communicate effectively, streamlining the setup process and minimizing errors.
Simple Network Management Protocol (SNMP) plays a central role in real-time monitoring and troubleshooting. By enabling communication among diverse devices, SNMP provides a common language for network management systems. This allows administrators to gather critical data on performance metrics such as CPU utilization and bandwidth usage, ensuring proactive issue resolution.
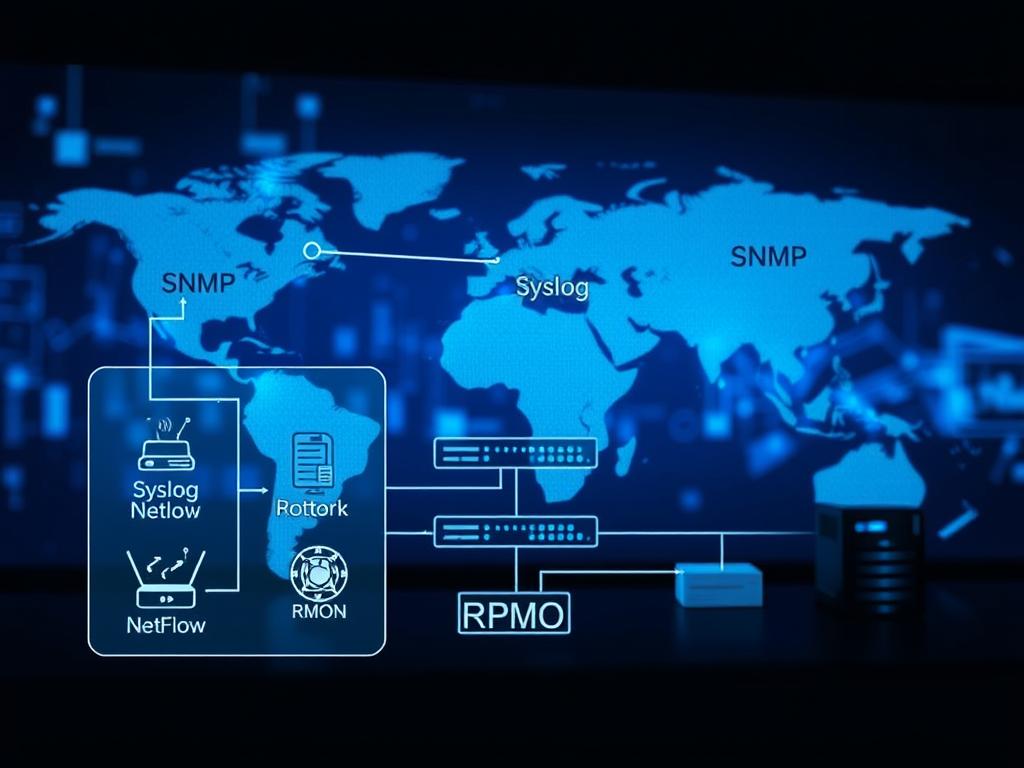
SNMP’s role extends to maintaining network stability, ensuring that applications and services function optimally by keeping network devices healthy. With versions like SNMP V2c and SNMP V3, the protocol has evolved to meet modern monitoring needs, offering enhanced security and efficiency.
Together, DHCP and SNMP provide network administrators with the control and visibility needed to manage complex systems effectively. Consistent management protocols are essential for maintaining network stability and performance, ensuring reliable communication across all connected devices.
“A well-managed network is the backbone of any successful organisation, enabling efficient communication and data exchange.”
Network Security Protocols: Ensuring Safe Communication
Security is paramount in today’s digital world. Network security protocols play a vital role in safeguarding data during transmission, ensuring confidentiality and integrity. These protocols are essential for protecting sensitive information from unauthorised access and cyber threats.
HTTPS, SSL/TLS and Secure Data Transmission
HTTPS, combined with SSL/TLS, is a cornerstone of secure web communication. SSL/TLS creates an encrypted channel, protecting data from eavesdropping and tampering. This encryption ensures that sensitive information, such as passwords and financial data, remains secure during transmission. HTTPS has become the standard for secure web traffic, replacing the insecure HTTP protocol.
Historically, older protocols like HTTP and Telnet transmitted data in plaintext, making them vulnerable to interception. Modern protocols like HTTPS and SFTP address these vulnerabilities by encrypting data. This shift has significantly enhanced security, particularly for online banking and e-commerce platforms where data protection is critical.
Secure email protocols such as POP3 and IMAP4 also play a crucial role in protecting communication. These protocols ensure that emails are transmitted securely, reducing the risk of interception. Similarly, secure file transfer protocols like SFTP and FTPS provide encrypted channels for transferring sensitive files, making them ideal for corporate environments where data security is paramount.
In summary, network security protocols are essential for maintaining the integrity and confidentiality of data. By adopting secure communication methods like HTTPS and encrypted file transfers, individuals and organisations can protect their sensitive information from evolving cyber threats. Investing in robust security measures is not just a precaution—it’s a necessity in today’s connected world.
Legacy Protocols and Evolving Technologies
Legacy protocols have long served as the foundation of digital communication, but the rapid evolution of technology has led to the development of more secure and efficient solutions. These older protocols, while groundbreaking in their time, often lacked the robust security and functionality required by today’s standards.
From Telnet to Modern Alternatives
Telnet, for instance, was once a widely-used protocol for remote access. However, its lack of encryption made it vulnerable to security breaches. Modern alternatives like SSH (Secure Shell) have since emerged, offering encrypted connections and enhanced protection against unauthorised access.
These advancements highlight the importance of adaptability in network communication. As cyber threats grow more sophisticated, so too must our protocols. The transition from outdated methods to contemporary solutions ensures that data transmission remains secure and efficient.
“The evolution of network protocols is not merely a matter of progress; it is a necessity in our increasingly connected world.”
This shift underscores the continuous innovation driving our digital landscape, ensuring that communication remains both safe and reliable for future generations.
Protocols in the OSI and TCP/IP Models
Understanding the frameworks that govern data communication is essential for grasping how protocols function. The OSI and TCP/IP models provide structured approaches to network communication, each with distinct layers that facilitate seamless data exchange.
A Layered Approach to Network Communication
The OSI model consists of seven layers, each handling specific tasks. For instance, the Application layer manages protocols like HTTP and FTP, enabling user interaction and file transfers. In contrast, the TCP/IP model consolidates these into a four-layer system, merging the Application, Presentation, and Session layers for simplicity.
| Model | Layers | Key Protocols |
|---|---|---|
| OSI | 7 (Physical to Application) | HTTP, FTP, TCP, IP, Ethernet |
| TCP/IP | 4 (Link, Internet, Transport, Application) | HTTP, FTP, DNS, TCP, UDP, IP |
Protocols like TCP and UDP operate at the Transport layer, ensuring data transfer reliability and efficiency. The OSI model’s Data Link layer uses Ethernet for device connections, while the TCP/IP model’s Internet layer relies on IP for routing. This layered structure ensures coherence between network devices, facilitating efficient message transmission and error handling.
In summary, both models provide frameworks for understanding protocol interactions, each with unique strengths. The OSI model offers detailed layering, while TCP/IP is praised for its practicality. Together, they underpin modern network communication, ensuring data reaches its destination accurately and efficiently.
The Role of Protocols in Data Transmission
Protocols play a crucial role in organising data transmission over the internet, ensuring accurate delivery of information across connected devices. Each computer is assigned a unique address, enabling precise routing of data packets to their intended destinations.
These addresses operate much like postal codes, guiding data through the internet’s complex network. Protocols such as Internet Protocol (IP) manage the routing process, ensuring that information reaches the correct device efficiently. This systematic approach prevents data loss and ensures integrity during transmission.

In real-world scenarios, effective data transmission is vital for operational efficiency. For instance, in banking systems, protocols ensure secure and rapid transaction processing. Similarly, in healthcare, accurate data transmission is critical for patient record management and telemedicine services.
Without these protocols, the internet would struggle to function, leading to frequent data loss and misdelivery. Thus, protocols are indispensable in maintaining the reliability and security of digital communication in our increasingly connected world.
Choosing the Right Protocol for Applications
When selecting a protocol for your application, several factors come into play to ensure optimal performance and security. The primary considerations include the specific requirements of your application, the type of network in use, and the need for reliability, speed, and security.
Factors Influencing Protocol Selection
The choice of protocol is heavily influenced by the nature of the application and the environment in which it operates. For instance, applications requiring high reliability benefit from TCP, which ensures ordered and lossless data delivery. On the other hand, applications prioritising speed, such as real-time streaming or online gaming, often leverage UDP for its efficiency, even though it does not guarantee delivery.
The type of network also plays a significant role in protocol selection. Small office networks may utilise simple LAN protocols such as Ethernet, while large enterprise networks might require more complex solutions like MPLS for WAN connectivity. Wireless environments often necessitate protocols like Wi-Fi for efficient data transmission.
Best Practices for Protocol Selection
When evaluating protocols, consider features, functions, costs, and compatibility. For secure communication, encryption protocols like SSL/TLS are essential, especially for sensitive data transmission. For efficiency, HTTP/2 offers improved performance over its predecessor, making it ideal for fast data exchange.
Reliability is crucial in scenarios where data loss could have significant consequences. TCP is the preferred choice here due to its guaranteed delivery. However, in applications where speed is paramount, such as live broadcasts or video conferencing, UDP’s multicast capabilities provide efficient data transfer to multiple clients simultaneously.
Practical Tips for IT Professionals
IT professionals should test protocols under various conditions to ensure they meet specific needs. Monitoring performance, reliability, and compatibility is essential for maintaining optimal network operation. Regular updates to protocols like IPv4, SNMP, and HTTPS are necessary to keep pace with evolving network demands.
In summary, selecting the right protocol involves a careful balance of security, speed, and efficiency. By understanding the application requirements and network environment, professionals can choose protocols that enhance performance and maintain robust security standards.
Conclusion
In the ever-evolving landscape of digital communication, network protocols remain the cornerstone of efficient and secure data exchange. These standardized rules ensure that devices can communicate seamlessly, regardless of their hardware or operating system.
Throughout this article, we have explored the diverse roles of protocols such as TCP/IP and UDP. These systems are fundamental to modern networking, enabling reliable data transmission and high-speed communication. Understanding both legacy and modern protocols is essential for maintaining system efficiency and adapting to future advancements.
The User Datagram Protocol (UDP) continues to play a crucial role in supporting rapid data transfer, particularly in real-time applications like video streaming and online gaming. Its efficiency, despite not guaranteeing delivery, makes it indispensable in scenarios where speed is paramount.
Looking ahead, the evolution of network protocols will likely focus on enhanced security and adaptability. As cyber threats become more sophisticated, so too will the systems designed to protect our data. The future of networking lies in innovative protocols that balance speed, reliability, and robust security.
In conclusion, network protocols are not just technical jargon; they are the lifeblood of our connected world. Their continued development ensures that our systems remain efficient, secure, and capable of meeting the demands of tomorrow.
Frequently Asked Questions
Understanding network protocols can sometimes raise questions, especially for those new to the topic. Below are answers to some of the most frequently asked questions about network protocols and their applications.
What is ICMP, and why is it important? ICMP, or Internet Control Message Protocol, is a diagnostic tool used to monitor and troubleshoot network connectivity issues. It helps devices communicate error messages, such as when a server is unreachable or a route is down. ICMP is essential for identifying and resolving network problems efficiently.
How does the Hypertext Transfer Protocol (HTTPS) secure data? HTTPS encrypts data transmitted between web servers and browsers using SSL/TLS encryption. This ensures that sensitive information, like passwords and financial data, remains protected from unauthorised access during transmission. HTTPS has become the standard for secure web communication, replacing the less secure HTTP protocol.
What are the key differences between ICMP and HTTPS? While ICMP focuses on network diagnostics and error reporting, HTTPS is designed to secure data transmission. Both are vital for maintaining network stability and security, but they serve distinct purposes in the communication process.
For those interested in exploring these topics further, resources like ICMP and HTTPS provide detailed technical insights.
FAQ
What is the importance of protocols in computer networks?
Protocols are essential as they define the rules for data transmission, ensuring devices can communicate effectively. They enable reliable data transfer, error detection, and efficient resource management across the network.
What is the difference between TCP and UDP?
TCP (Transmission Control Protocol) is a connection-oriented protocol that ensures reliable data delivery with error-checking and flow control. UDP (User Datagram Protocol) is connectionless, prioritising speed over reliability, making it ideal for real-time applications like video streaming.
How do devices locate each other on a network?
Devices use IP addresses and routing tables to identify and locate each other. These addresses act as unique identifiers, ensuring data packets reach their intended destination.
What are the most common types of network protocols?
Common protocols include HTTP (Hypertext Transfer Protocol) for web communication, FTP (File Transfer Protocol) for file sharing, SMTP (Simple Mail Transfer Protocol) for email, and DNS (Domain Name System) for translating domain names to IP addresses.
How do security protocols protect data?
Security protocols like HTTPS, SSL/TLS, and SFTP encrypt data during transmission, preventing unauthorised access. They ensure secure communication by authenticating devices and safeguarding sensitive information.
What role does ICMP play in network communication?
ICMP (Internet Control Message Protocol) is used for diagnostic and error-reporting functions. It helps devices communicate network issues, such as unreachable destinations or packet errors, ensuring network management and troubleshooting.
Are all protocols still relevant in modern networking?
While many legacy protocols like Telnet have been replaced by more secure alternatives, others like TCP/IP remain foundational. The evolution of technology ensures that only protocols meeting modern demands for security and efficiency are widely adopted.